The Current State of Cyber Security and Its Limitations
Over the past 20-plus years, Information Security, Information Assurance, and now Cyber Security have increasingly become an exercise in managing risk to the point of almost abandoning mitigating vulnerabilities. We've relied on organizations & consulting professionals who have focused on using legacy techniques & stacking redundant symmetric authentication factors to avoid meaningful change.

Security by obscurity, which has failed in the past, has once again become good enough to satisfy risk management objectives. The result is that we continue to conduct business online without confidence that the online credentials being used are accurately associated with a specific entity. We still offer little or no mechanism to confidently know the difference between legitimate & illegitimate parties/ entities transacting - while agreeing that they are the most significant vulnerability.
The Impact of Anonymity and Outdated Strategies on Cyber Security
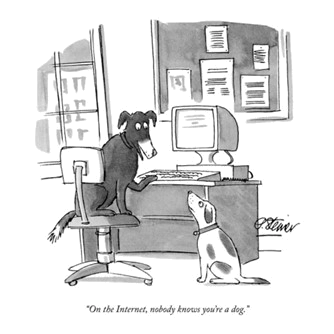
[Peter Steiner has been reproduced from page 61 of July 5, 1993 issue of The New Yorker, (Vol.69 (LXIX) no. 20) only for academic discussion, evaluation, research and complies with the copyright law of the United States as defined and stipulated under Title 17 U. S. Code].
Yet a general lack of accountability in our government and society has led to the evolution of an information super-highway that offers unchecked anonymity for criminal activity at the scope and speeds beyond human control. So why does our federal government and industries continue to deploy technology that is much older than the legislation in place to protect our privacy? We have recognized the problem but continue to rely on outdated strategies and tactics, causing an intellectual void within the Information Assurance/ Cyber Security industry. This has resulted in exponentially increased amounts of fraud in private and public transactions and weakened our economy and national security.
Medicare is often criticized for a continued practice, often called “pay and chase,” in which a Medicare provider is paid and then chased down later for a refund if an error or fraud is detected. More often than not, the improper payment is never recouped. This strategy is not unique to Medicare; our entire Cyber Security strategy has subjugated current solutions to address vulnerabilities by trying to block constantly changing malware and attempting to recognize previously recorded "signatures" of successful attacks are failed solutions. While these monitoring solutions address and potentially mitigate recurring penetrations, it is well documented that even a single hack can be catastrophic.
Inadequate Cyber Security Approaches and the Cost of Data Breaches
While the median number of days those attackers were present on a victim’s network before being discovered has dropped significantly over the past decade, the amount of damage being done continues to grow. According to the IBM Cost of a Data Breach Report 2021, Data breach costs rose to USD 4.24 million, the highest average total cost in reports the 17-year history. The average cost was USD 1.07 million higher in breaches where remote work (which is also estimated to grow was a factor in causing the breach. And, the most common initial attack vector is still compromised credentials.
The Growing Threats in a World of Quantum Computing and IoT
An enterprise attacker that plants a software agent can exfiltrate a huge amount of data long before detection. This will become worse as quantum computing matures. In the case of ransomware, it is ironic that the technology we invented to prevent unapproved access to our data and information is much more effectively being used by attackers to keep us from accessing our own data and information. With the proliferation of the Internet of Things (IoT), the number of anonymous endpoints we are forced to "trust" on the Internet is growing at an alarming rate. Cyber Security must change the focus to ensure access and privileges are limited to approved users, devices, and IoT.
Cybersecurity Maturity Model Certification (CMMC) - A Step Forward in Securing the Supply Chain

The model focuses on existing FAR requirements and provides guidance, particularly for small and medium-sized businesses that desire to do, or continue to do, business with the Federal Government. 
The Future of Cyber Security and Compliance for Federal Contractors
The DFARS ruling is expected to affect DoD acquisitions as soon as FY 2023/ 2024. But all DIB organizations are already contractually obligated to comply with NIST SP 800-171.
So, every DIB organization needs to be asking today:
- Are we sufficiently and adequately managing cybersecurity threats now?
- What challenges do we need to overcome to create a cybersecurity cultural change for ourselves and our supply chain?
- What are the most significant changes that CMMC will bring to us that we must prepare for now?
- Does the CMMC Model align with other cybersecurity frameworks we are involved with?
- Who can be the change agent for our organization?
Visit our CMMC 2.0 Certification FAQ to read about the CMMC Certification Pathway.


